Canoeboot project
- Home
- About
- FAQ
- Canoeboot vs GNU Boot
- Download
- Install
- Docs
- News
- Bugs
- Send patch
- Contact
- Back to libreboot.org
English | Deutsch | Français | Italiano | українська | 简体中文
The Canoeboot project provides free, open source (libre) boot firmware based on coreboot, replacing proprietary BIOS/UEFI firmware on specific Intel/AMD x86 and ARM based motherboards, including laptop and desktop computers. It initialises the hardware (e.g. memory controller, CPU, peripherals) and starts a bootloader for your operating system. GNU+Linux and BSD are well-supported. Help is available via #canoeboot on Libera IRC.
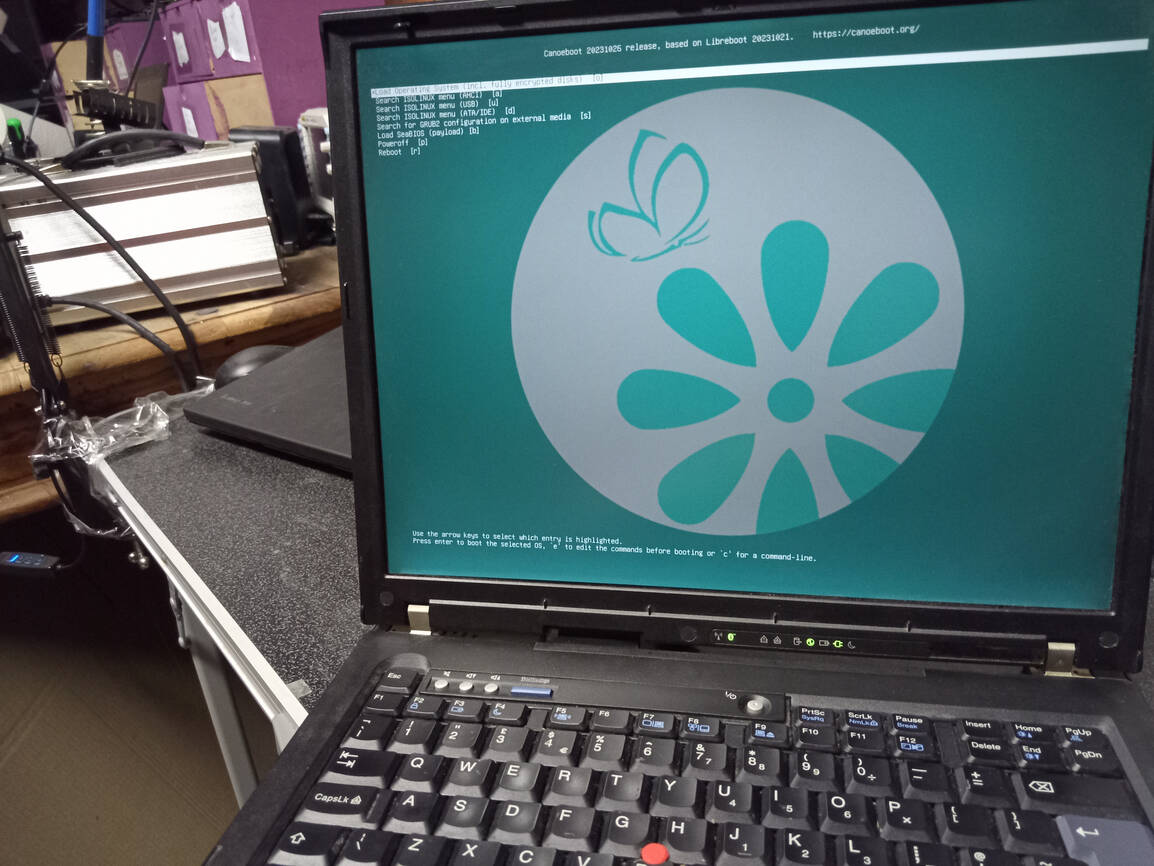
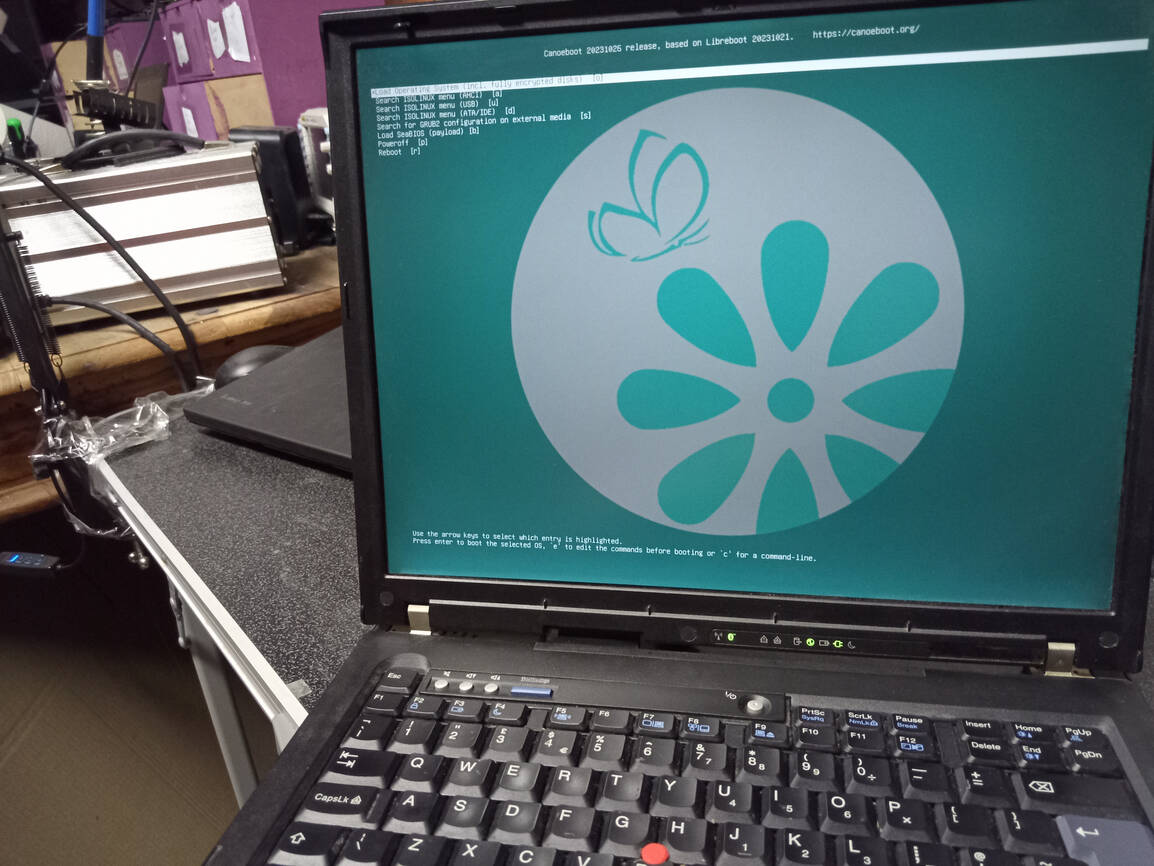
NEW RELEASE: The latest release is Canoeboot 20231107, released on 7 November 2023. See: Canoeboot 20231107 release announcement.
Canoeboot was originally named nonGeNUine Boot, provided as a proof of concept for the GNU Boot or gnuboot project to use a more modern Libreboot base, but they went in their own direction instead. Canoeboot development was continued, and it maintains sync with the Libreboot project, as a parallel development effort. See: How are Canoeboot releases engineered?
Canoeboot adheres to the GNU Free System Distribution Guidelines as policy, whereas Libreboot adheres to its own Binary Blob Reduction Policy. Canoeboot and Libreboot are both maintained by the same person, Leah Rowe, sharing code back and forth.
Why should you use Canoeboot?
Canoeboot gives you freedoms that you otherwise can’t get with most other boot firmware, plus faster boot speeds and better security. It’s extremely powerful and configurable for many use cases. Canoeboot is a special fork of Libreboot, maintained in parallel to it by the same developer (Leah Rowe); Canoeboot complies with the GNU Free System Distribution Guidelines, whereas Libreboot adopts a more pragmatic Binary Blob Reduction Policy. Consequently, Canoeboot only supports a very limited subset of hardware from coreboot that is known to boot without binary blobs. Many other boards in coreboot require binary blobs for things like memory controller initialisation. Canoeboot removes binary blobs from coreboot and U-Boot, which are then provided “de-blobbed” in releases.
We believe the freedom to study, share, modify and use software, without any restriction, is one of the fundamental human rights that everyone must have. In this context, software freedom matters. Your freedom matters. Education matters. Right to repair matters. Many people use proprietary (non-libre) boot firmware, even if they use a libre OS. Proprietary firmware often contains backdoors, and can be buggy. The Canoeboot project was founded in October 2023, with the express purpose of making coreboot firmware accessible for non-technical users.
The Canoeboot project uses coreboot for hardware initialisation. Coreboot is notoriously difficult to install for most non-technical users; it handles only basic initialization and jumps to a separate payload program (e.g. GRUB, Tianocore), which must also be configured. Canoeboot solves this problem; it is a coreboot distribution with an automated build system that builds complete ROM images, for more robust installation. Documentation is provided.
Canoeboot is not a fork of coreboot
In fact, Canoeboot tries to stay as close to stock coreboot as possible, for each board, but with many different types of configuration provided automatically by the Canoeboot build system.
In the same way that Alpine Linux is a Linux distribution, Canoeboot is a coreboot distribution. If you want to build a ROM image from scratch, you otherwise have to perform expert-level configuration of coreboot, GRUB and whatever other software you need, to prepare the ROM image. With Canoeboot, you can literally download from Git or a source archive, and run make, and it will build entire ROM images. An automated build system, named cbmk (CanoeBoot MaKe), builds these ROM images automatically, without any user input or intervention required. Configuration has already been performed in advance.
If you were to build regular coreboot, without using Canoeboot’s automated build system, it would require a lot more intervention and decent technical knowledge to produce a working configuration.
Regular binary releases of Canoeboot provide these ROM images pre-compiled, and you can simply install them, with no special knowledge or skill except the ability to follow simplified instructions, written for non-technical users.
Markdown file for this page: https://canoeboot.org/index.md
Subscribe to RSS for this site
This HTML page was generated by the Untitled Static Site Generator.